Decoding Your Company’s Cyberattack Response Plan
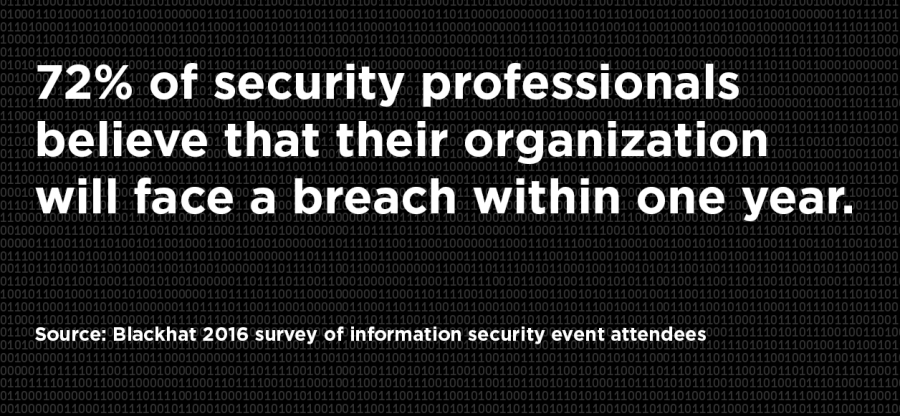
A prevention-only strategy is no longer sufficient for organizations hoping to remain proactive in protecting their data. By creating an incident-response plan, you can give leaders across the organization the agency to mobilize in the event of an attack.
Due to the sophistication and adaptability of cybercriminals, a digital hack within the lifetime of an organization is nearly inevitable. If anything can be taken away from the Equifax data breach, which compromised the information of 143 million American consumers, it’s that the onus of digital security belongs to all leaders of a company.
Terry Kurzynski, senior partner at HALOCK Security Labs, cautions his fellow leaders to take a realistic approach and consider both prevention and response tactics when drafting a cyber preparation plan. “The industry needs to invest more in incident response capabilities versus only on protection investments,” he says.
The formalization of an incident response plan helps document these steps. The plan should include those tasks that must be done within minutes and hours, rather than days, and be disseminated and understood by all relevant leaders. Doing so will reduce the precocious time between a digital compromise and remediation for organizations and their clients. These plans will vary by organization, but the following steps capture best practices for responding to a breach.
Survey: Conduct an overall survey that assesses the damage, discovering and remedying the sources of the vulnerability, and identifying the attackers.
Limit: Surveying the hack is the first step to limiting potential damage and reducing the company’s chance of liability. The next step of isolating any compromised systems and filtering traffic away from the breach will further reduce the chance of additional damage.
Record: In every industry, especially those where sensitive data is protected by law, documentation is essential. Following a hack, you must record the extent of the damage, including any effects for the organization or its clients, as well as identifying any potential disruptions to service offerings.
Engage: It’s important to inform several outside parties following a hack. Organizations who should be notified include law enforcement—including local police and the FBI—and the district attorney’s office. The earlier this is done, the less chance of public lawsuits and PR mishaps.
Notify: Beyond legal authorities, several other groups must be notified. This list includes clients, vendors, and any other parties who could have been affected by the hack. This is also a good opportunity to contact legal counsel who specializes in cybersecurity matters.
Learn: With cyber hacks all but guaranteed in today’s digital first world, it’s critical for organizations and their clients to document the circumstances before, during, and after anything happens. Documentation should be followed up with proactive company-wide training.
For a look at the legal side of cybersecurity, download our white paper, “The General Counsel’s Guide to Digital Defense.”
